Middleware
Unlocker Middleware (Lock/Unlock RFID Tags + EPC Updates)
Unlocker middleware to lock/unlock RFID tags, update desired EPC, import passwords from CSV, and access tag details securely with audit logs.
-
CSV-driven
Batch operations
import access passwords and workflows
-
lock / unlock
Core actions
plus EPC and memory operations
-
auditability
Safety goal
trace every write and status change
Key entities: EPC update · Access password · Kill password · Tag memory · Audit logs
What is unlocker middleware?
Lock and unlock tags (controlled workflow)
Update desired EPC and tag details
Read passwords from CSV and operate at scale
Representative outcome
Problem
Manual tag security changes led to inconsistent states and rework.
Solution
Unlocker middleware with CSV imports, EPC updates, and lock/unlock workflows with verification.
Results
- Fewer failed writes and rework cycles
- Consistent security state enforcement
- Traceable audit logs for changes
Frequently asked questions
Can I bulk-update tags using a CSV file?
Is this safe for production tags?
Can it show tag details before writing?
Discover more
You may also like
Hand-picked articles and pages worth your time next.

RFID standards
RFID standards primer: ISO 18000-6C, GS1 EPC, NFC HF, and what Indian enterprises should verify before procurement.

Stock management middleware
Handheld-driven stock updates and reconciliation—pairs well with tag commissioning and EPC programs.
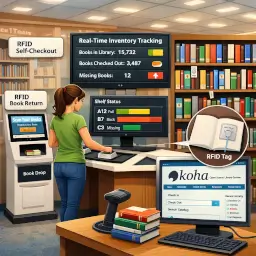
Koha handheld middleware
Handheld middleware for Koha: register items, find books, and streamline issue/return with RFID reads.

Access control middleware
Log device events, trigger workflows, and normalize access control integrations.